Authored by Shanaka Anslem Perera via Substack,
The four trillion dollars in institutional capital positioned for stable UK-China relations rests on an assumption that died in a Chengdu server room sometime around 2019. The assumption is that espionage between major powers operates within understood boundaries, that telecommunications infrastructure is contested but not compromised, that the surveillance systems Western governments built to watch their citizens cannot be turned around to watch them. The assumption has been falsified. What follows is the complete mechanism of how China’s Ministry of State Security achieved persistent access to the private communications of three British Prime Ministers’ closest advisers, the phones of a US President-elect, and the wiretap systems that were supposed to catch them doing it. The positioning implications are immediate. The framework is permanent.
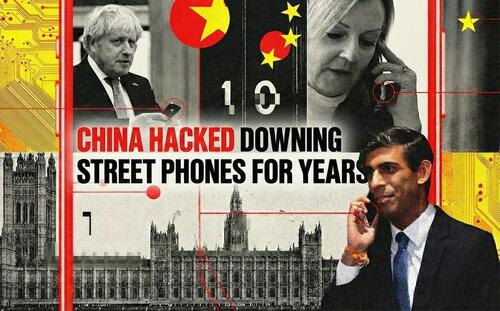
On January 26, 2026, The Telegraph disclosed that Chinese hackers had penetrated right into the heart of Downing Street, compromising mobile communications of senior officials across the Johnson, Truss, and Sunak administrations. The story was buried on page seven, treated as a technology curiosity. It was, in fact, a solvency event for the Western intelligence alliance. Not because phones were hacked, which happens, but because of how they were hacked: by weaponizing the very surveillance infrastructure that Western governments mandated for their own intelligence agencies. The Communications Assistance for Law Enforcement Act in the United States and the Investigatory Powers Act in the United Kingdom require telecommunications carriers to build backdoors into their networks for court-ordered wiretapping. Chinese state hackers found those backdoors. And walked through them.
The intelligence value is almost impossible to overstate. For approximately four years, operators linked to the MSS’s Chengdu bureau had the capability to see not just who British officials were calling, but whom the FBI was investigating, which Chinese operatives were under surveillance, what the United States knew about Beijing’s activities, and when counterintelligence was getting close. They could geolocate millions of individuals. They could record phone calls at will. They compromised the surveillance of their own surveillers, achieving the counterintelligence equivalent of reading the other side’s playbook while the game was in progress.
What follows is the institutional playbook. The positions are already being built.
The Backdoor That Swung Both Ways
The story of Salt Typhoon is not fundamentally a story about hacking. It is a story about architecture. Specifically, it is a story about what happens when governments mandate that their surveillance systems include single points of failure, then assume those points will only fail in their favor.
In 1994, the United States Congress passed the Communications Assistance for Law Enforcement Act, requiring telecommunications carriers to design their networks with built-in capabilities for government wiretapping. The law emerged from FBI concerns that digital switching technology would render traditional surveillance impossible. CALEA’s solution was elegant in its naivety: force every carrier to build a standardized interface through which law enforcement could access communications pursuant to court order. The interface would be secure because it would be secret, protected by access controls, audited by compliance regimes. No adversary would find it because no adversary would know to look.
Twenty-two years later, the United Kingdom enacted the Investigatory Powers Act 2016, colloquially known as the Snooper’s Charter. It went further than CALEA, mandating that technology companies retain communications data and provide access mechanisms for intelligence agencies. The architecture was the same: centralized access points designed for authorized users, protected by the assumption that authorized users would be the only ones using them.
Salt Typhoon was the adversarial audit that the system failed.
The Chinese operators did not need to hack individual phones, which would have been noisy and detectable. They did not need to intercept communications in transit, which would have required breaking encryption. They hacked the wiretap system itself. Once inside the CALEA infrastructure at AT&T, Verizon, and Lumen Technologies, they had access to everything the FBI had access to: call metadata showing who contacted whom and when, geolocation data derived from cell tower triangulation, the actual content of unencrypted calls and texts, and most devastatingly, the database of active surveillance requests. They could see whom the United States government was watching. They could see if they themselves were being watched.
The vulnerability was not a bug in the architecture. It was the architecture.
For decades, cryptographers and privacy advocates warned that there is no such thing as a backdoor only good guys can use. A vulnerability is a vulnerability. If it exists, a sufficiently motivated and resourced adversary will find it. The NSA and GCHQ and FBI dismissed these warnings as theoretical, academic, disconnected from operational reality. Law enforcement’s access needs are legitimate. But Salt Typhoon demonstrated empirically that the risks of mandated backdoors extend to everyone, including the governments that mandated them.
The irony approaches the unbearable. As Salt Typhoon was being discovered in late 2024, the UK government was pressuring Apple to weaken iMessage encryption under the Investigatory Powers Act. The argument was the same one that produced CALEA: law enforcement needs access, and carefully controlled access can be kept secure. Apple reportedly disabled certain features for UK users rather than comply. At precisely the same moment, as The Telegraph would later reveal, Chinese operators were reading communications from the heart of Downing Street through the access points the UK government had mandated.
The technical community has a name for this: the security paradox. Systems designed to enable surveillance become targets for adversary surveillance. The more access points you create for your own agencies, the more attack surface you expose to foreign agencies. The debate between security and privacy was always a false binary. The real tradeoff was between surveillability by your government and surveillability by everyone’s government.
Salt Typhoon collapsed that tradeoff into a single devastating data point.
The Kill Chain That Cannot Be Killed
Understanding what happened requires understanding how telecommunications networks actually function, not how they appear in policy documents.
A modern telecom network is not a monolithic system but a layered architecture spanning edge devices that connect to the public internet, core routing infrastructure that moves packets between networks, administrative systems that manage configurations and access, billing and customer data platforms, and lawful intercept systems that process surveillance requests. Each layer has its own attack surface. Salt Typhoon targeted the layer that matters most: the edge devices that control everything else.
The primary intrusion vector was a pair of vulnerabilities in Cisco IOS XE, the operating system running on millions of enterprise routers and switches worldwide. CVE-2023-20198, with a perfect 10.0 CVSS severity score, allowed an unauthenticated remote attacker to create an administrator account with Level 15 privileges, the highest access level on Cisco devices. CVE-2023-20273 enabled command injection that elevated those privileges to root access on the underlying Linux operating system. Chain them together and an attacker can create a god-mode account on any exposed Cisco device, then execute arbitrary code with full system control.
The vulnerabilities were disclosed in October 2023. Cisco issued patches. Many telecommunications operators delayed patching due to operational constraints that made rapid remediation nearly impossible.
This dynamic is not incompetence, though it resembles incompetence. Telecommunications infrastructure operates under pressures that create structural patch delays. These networks run 24 hours a day, 365 days a year. Downtime is measured in lost revenue and regulatory penalties. Patching a core router requires scheduling maintenance windows, testing updates in lab environments, coordinating with interconnected carriers, and accepting the risk that the patch itself introduces instability. For many operators, the calculation becomes: known theoretical vulnerability versus certain operational disruption. They chose the theoretical vulnerability. Salt Typhoon chose them.
Recorded Future’s Insikt Group documented the campaign exploiting over one thousand Cisco devices globally between December 2024 and January 2025. But the truly alarming finding was that attackers also exploited CVE-2018-0171, a vulnerability in Cisco Smart Install that had been patched seven years earlier. Some devices in critical telecommunications infrastructure had not been updated since 2018. The attack surface was not the frontier of zero-day exploitation. It was the accumulated technical debt of an industry that treated security as a cost center.
Once inside, Salt Typhoon deployed a sophisticated persistence mechanism designed to survive exactly the remediation attempts carriers would eventually undertake. The primary implant, documented by Trend Micro researchers under the name GhostSpider, operated entirely in memory without touching disk, evading traditional antivirus that scans for malicious files. It used DLL hijacking to execute within the context of legitimate processes, bypassing application whitelisting. Communications with command-and-control servers were encrypted and disguised as normal HTTPS traffic, blending with legitimate web activity.
The deeper persistence came from Demodex, a kernel-mode rootkit that modified the Windows operating system at its lowest level. Demodex hooked into system calls to hide its own processes, network connections, and registry entries from administrators running diagnostic commands. An operator investigating a compromised system would see nothing amiss because the rootkit was filtering what they could see. The malware achieved what the cybersecurity industry calls god-mode persistence: invisibility so complete that the only certain remediation is physical hardware replacement.
On Cisco devices specifically, the attackers exploited the Guest Shell, a Linux container environment designed for running legitimate management scripts. By injecting malicious code into this trusted container, they achieved persistence that survived standard reboots and even operating system reimaging. The infection lived below the level that normal administrators could access. It was not hiding in the house. It had become part of the foundation.
The operational sophistication extended to exfiltration. Salt Typhoon deployed a custom tool called JumbledPath that enabled packet capture across multiple network hops while simultaneously clearing logs and disabling logging along the capture path. They could intercept traffic without leaving forensic evidence of the interception. They modified Access Control Lists on compromised switches to explicitly permit their command-and-control IP addresses, ensuring their backdoors remained reachable even as security teams updated firewall rules. They created Generic Routing Encapsulation tunnels to route stolen data through compromised infrastructure, making the exfiltration appear as legitimate network traffic.
According to Cisco Talos analysis, the average dwell time before discovery was 393 days. One environment showed attackers maintaining presence for over three years. Three years of access to telecommunications infrastructure that carries the communications of governments, corporations, and private citizens. Three years of watching the watchers.
Inside the Chengdu Hacker-for-Hire Marketplace
Attribution in cyber operations is notoriously difficult. Attackers route through compromised infrastructure in multiple countries, use commodity malware available to any buyer, and deliberately plant false flags suggesting different national origins. The intelligence community has learned hard lessons about premature attribution.
Salt Typhoon attribution does not suffer these ambiguities. It is among the most thoroughly documented cases of state-sponsored cyber operations in the public record.
The US Treasury Department sanctioned Sichuan Juxinhe Network Technology Co., Ltd. on January 17, 2025, identifying it as a Chengdu-based cybersecurity company with direct involvement in the Salt Typhoon cyber group. The language was unusually specific for a sanctions designation, which typically uses more cautious phrasing. Treasury stated that the Ministry of State Security has maintained strong ties with multiple computer network exploitation companies, including Sichuan Juxinhe. The implication was unmistakable: this was not a rogue actor tangentially connected to Chinese intelligence. This was an MSS operation executed through contractor infrastructure.
Chengdu has emerged as the primary hub of China’s offensive cyber contractor ecosystem, a distinction it shares with no other Chinese city to the same degree. The reasons are structural. Sichuan University and Chengdu University of Information Technology produce a steady pipeline of computer science graduates with the technical skills offensive operations require. The provincial government offers tax incentives for high-tech enterprises that attract cybersecurity firms. The MSS’s Chengdu bureau has historically been aggressive in recruiting and contracting local talent. The result is a geographic concentration of capability that the intelligence community has tracked for over a decade.
Sichuan Juxinhe is not an isolated entity but part of an interconnected ecosystem. Treasury’s designation also referenced Beijing Huanyu Tianqiong Information Technology Co., Ltd. and Sichuan Zhixin Ruijie Network Technology Co., Ltd. as associated entities. These firms share corporate registration patterns, overlapping personnel, and technical infrastructure in ways that suggest coordinated rather than independent operation.
The ecosystem became dramatically more visible in February 2024, when over five hundred internal documents from i-SOON (Sichuan Anxun Information Technology Co., Ltd.) appeared on GitHub in one of the most significant leaks of Chinese cyber operations ever recorded. The documents revealed a hacker-for-hire marketplace where private firms bid on government contracts to compromise specific targets. Price lists showed costs for different levels of access. Marketing materials advertised tools for hacking Twitter, Gmail, WeChat, and Telegram. Target lists included governments in India, Thailand, Vietnam, South Korea, and NATO member states. The operational picture was unmistakable: China’s cyber espionage apparatus operates significantly through private contractors who compete for MSS and PLA business.
The i-SOON leak provided a Rosetta Stone for understanding how Salt Typhoon operates. Domain registration patterns used by i-SOON matched those observed in Salt Typhoon infrastructure. Malware families overlapped. The corporate relationship between i-SOON and other Chengdu firms explained how capabilities and targeting information might flow between ostensibly separate entities.
The UK government reached the same conclusion. On December 9, 2025, Foreign Secretary Yvette Cooper announced sanctions against Integrity Technology Group and Sichuan Anxun Information Technology (i-SOON) for activities against the UK and its allies that impact our collective security. The 13-nation joint advisory released in August 2025 explicitly attributed the campaign to MSS-linked private contractors, co-signed by agencies from the United States, United Kingdom, Australia, Canada, New Zealand, Germany, Japan, and five other nations.
The evidence supporting attribution is overwhelming: convergent technical indicators across multiple intelligence services, targeting patterns aligned with MSS priorities rather than financial motivation, sanctions from two G7 governments naming specific companies, a leaked document trove revealing operational details, and multi-national intelligence consensus among powers with no incentive to coordinate false attribution.
Chinese Foreign Ministry spokesperson Guo Jiakun dismissed the allegations as unfounded and irresponsible smears and slanders, claiming China stands against hacking and fights such activities in accordance with the law. Chinese state media advanced the counter-narrative that Salt Typhoon accusations represent US efforts to secure congressional appropriations rather than genuine intelligence findings. The Global Times characterized the accusations as a farce of US smear tactics against China.
These denials represent diplomatic necessities. They do not survive contact with the documented evidence.
The Crown Jewels: Three Prime Ministers’ Inner Circles Exposed
The targeting profile of Salt Typhoon reveals strategic intent far beyond conventional espionage.
In the United States, nine telecommunications carriers have been confirmed compromised: Verizon, AT&T, T-Mobile, Lumen Technologies, Spectrum (Charter Communications), Consolidated Communications, Windstream, Viasat, and at least one additional unnamed provider. Senator Mark Warner, chairman of the Senate Intelligence Committee, characterized it as the worst telecom hack in our nation’s history. The scope comparison is instructive. SolarWinds, the Russian supply chain compromise discovered in December 2020, affected approximately 18,000 organizations with deep penetration of roughly 100. Salt Typhoon compromised over 200 companies across 80 countries.
The data accessed falls into two categories with very different strategic implications.
The first category is bulk metadata: call detail records showing who contacted whom, when, and for how long, plus geolocation data derived from cell tower connections. Former Deputy National Security Advisor Anne Neuberger confirmed that attackers gained capabilities to geolocate millions of individuals. Metadata reveals patterns invisible in content alone. If a senior Treasury official calls a specific BP executive three times in one night before a North Sea oil announcement, Beijing knows the policy shift before the Cabinet does. Mapping communication networks reveals the actual decision-making structure of governments, which often differs substantially from organizational charts.
The second category is targeted content interception. Fewer than 100 individuals had actual call content and text messages directly compromised, but those individuals included Donald Trump, JD Vance, and senior staff from the Harris campaign during the 2024 presidential election. Congressional staff from the House China Committee, Foreign Affairs Committee, Armed Services Committee, and Intelligence Committee were accessed in breaches detected in December 2025, according to the Financial Times. The targeting was not random. It was surgical.
The United Kingdom penetration, disclosed by The Telegraph on January 26, 2026, reached right into the heart of Downing Street. The National Cyber Security Centre confirmed observing a cluster of activity targeting UK infrastructure since 2021. Aides to Prime Ministers Boris Johnson, Liz Truss, and Rishi Sunak had their communications compromised across a three-year period that included the COVID-19 pandemic response, the Ukraine war’s escalation, and critical UK-China trade negotiations.
Whether the Prime Ministers’ personal devices were directly compromised remains publicly unclear. The distinction may matter less than it appears. In a telecom network intrusion, attackers do not need to compromise individual devices. They compromise the network itself, intercepting communications as they transit carrier infrastructure. The Prime Minister’s phone may have been perfectly secure. The calls it made were not.
The strategic timing compounds the damage. The 2021-2024 window included decisions on Huawei’s role in UK 5G infrastructure, the AUKUS security pact formation, Hong Kong sanctions policy, and bilateral trade negotiations with Beijing. Chinese intelligence had real-time visibility into British decision-making during discussions where China’s interests were directly at stake. The information asymmetry is staggering.
Australia was similarly targeted. ASIO Director-General Mike Burgess confirmed in November 2025 that Salt Typhoon attempted to access Australia’s critical infrastructure, including telecommunications networks. Canada experienced confirmed breach of at least one unnamed telecom in February 2025. The campaign extended beyond the Five Eyes core: a South African provider was reportedly compromised via Cisco platforms, Southeast Asian telecoms detected new malware variants, and European telecommunications organizations identified intrusion attempts as late as October 2025.
The counterintelligence implications are the most damaging aspect, though the least publicly discussed.
By accessing CALEA systems, Salt Typhoon operators could see the database of active wiretap requests. They knew whom the FBI was investigating. If MSS operatives in the United States were under surveillance, Beijing could pull them out before arrests occurred. If FBI investigations were approaching sensitive Chinese assets, Beijing could warn them. If counterintelligence operations were building cases against Chinese technology companies or influence operations, Beijing could see the evidence accumulating.
This is the counterintelligence nightmare: your surveillance apparatus becomes the adversary’s intelligence source. The FBI was not just failing to catch Chinese spies. It was showing China exactly where to find its exposed spies before the FBI could catch them.
The Hidden Correlation That Risk Models Never Saw
Systems approaching critical transitions exhibit a distinctive signature that financial risk models systematically miss. Surface metrics remain stable while underlying pressure accumulates. Correlations appear benign precisely because the stress is building uniformly across connected components. Then the transition happens not gradually but all at once, in a cascade that propagates faster than response mechanisms can activate.
The physics of phase transitions describes the phenomenon with precision. Water remains liquid as it cools, molecules slowing gradually, temperature dropping predictably. Then at exactly zero degrees Celsius, the system reorganizes instantaneously into a crystalline structure. The transition is discontinuous. Nothing in the gradual cooling predicted the sudden restructuring.
Salt Typhoon’s propagation through global telecommunications followed this pattern. The Global Cyber Alliance documented 72 million attack attempts from China-origin IP addresses against telecommunications infrastructure worldwide between August 2023 and August 2025. The number is not the important part. The distribution is. Rather than concentrating on a few high-value targets, the campaign probed systematically across the entire internet-facing surface of telecom networks in 80 countries. When one vector failed, others succeeded. The attack percolated through the network of networks, finding paths of least resistance through unpatched devices, legacy systems, and accumulated technical debt.
The 80-country spread was not a bug or scope creep. It was the exploitation of network topology itself. Telecommunications providers interconnect through peering relationships, shared vendors, inherited trust, and common infrastructure. Compromising one provider creates pivot points into connected providers. The attackers did not need to breach 80 countries independently. They needed to breach enough nodes that cascade dynamics carried the compromise further.
Financial risk models trained on historical correlations would have seen nothing unusual in the period before disclosure. Telecom stocks moved with normal volatility. Cybersecurity spending followed typical budget cycles. The correlation stability that risk managers found reassuring was measuring the pressure building uniformly, not the probability of release.
The parallel to credit markets before 2008 is instructive though imprecise. Mortgage-backed securities showed stable correlations because they were all exposed to the same underlying risk. The stability was the warning, not the comfort. When housing prices turned, the correlation snapped to one and everything moved together. The diversification that looked protective turned out to be concentration disguised.
Salt Typhoon exposed a similar hidden correlation in critical infrastructure. The assumption was that a breach of Verizon had no implications for BT, that American vulnerabilities were American problems, that European telecoms operated in a separate risk regime. The assumption was wrong. The same Cisco devices run everywhere. The same CALEA architecture creates the same vulnerability everywhere its analogues exist. The same contractor ecosystem targets everyone with the same tooling. The diversification across carriers and jurisdictions was illusory. They were all one network.
Five Eyes Fractures Under Pressure
The Five Eyes intelligence alliance, comprising the United States, United Kingdom, Canada, Australia, and New Zealand, represents the deepest and most institutionalized intelligence-sharing arrangement among Western democracies. Its origins in World War II signals intelligence cooperation have evolved into comprehensive collaboration on technical collection, analysis, and counterintelligence. Salt Typhoon tested this architecture as nothing has since its formation.
The initial response demonstrated the alliance’s coordination capabilities. The December 2024 Enhanced Visibility and Hardening Guidance for Communications Infrastructure was the first joint Five Eyes response to the breach. The August 2025 advisory expanded to 13 nations, co-sealed by 22 agencies attributing the campaign to specific Chinese companies with unprecedented multinational consensus. The coordination was real and consequential.
But the fractures were also visible.
UK officials pointedly stated that had American regulations matched British standards, we would have found it faster, we would have contained it faster. The criticism was technically accurate. The UK’s Telecommunications Security Act 2021 imposed security obligations on carriers that exceed CALEA requirements. But the same UK government pursuing those regulations was simultaneously pressuring Apple to weaken encryption under the Investigatory Powers Act, replicating exactly the architectural vulnerability that Salt Typhoon exploited. The internal contradiction was not resolved so much as ignored.
The regulatory divergence reflects deeper philosophical disagreements that Salt Typhoon intensified without settling. The FBI and CISA’s December 2024 recommendation that Americans use end-to-end encrypted messaging applications represented an extraordinary acknowledgment that carrier networks cannot be trusted. Yet both agencies have historically sought encryption backdoors for law enforcement access. The cognitive dissonance remained unaddressed: advocating for encryption to protect against foreign adversaries while seeking to weaken encryption for domestic law enforcement.
The FCC’s regulatory response exemplified the policy incoherence. In January 2025, the Commission proposed mandatory cybersecurity requirements including role-based access controls, multi-factor authentication, and vulnerability patching for telecommunications carriers. Then-Chairwoman Jessica Rosenworcel stated: In light of the vulnerabilities exposed by Salt Typhoon, we need to take action. In November 2025, the reconstituted FCC voted 2-1 to revoke those rules. Chairman Brendan Carr argued for an agile and collaborative approach over regulatory mandates. Commissioner Anna Gomez dissented: This FCC today is leaving Americans less protected than they were the day this breach was discovered.
The Cyber Safety Review Board investigation, established to provide an authoritative post-mortem on Salt Typhoon, was terminated in January 2025 when the incoming administration dismissed all members before their investigation concluded. The official lessons learned process stopped before identifying lessons.
Intelligence sharing itself became contested. Reports emerged in 2025 that DNI Tulsi Gabbard barred sharing certain intelligence with Five Eyes partners. While some former officials characterized concerns as faux outrage, noting that withholding occurs routinely, others warned of a chilling effect on critical intelligence sharing at precisely the moment coordination mattered most.
From a Chinese perspective, as expressed by state media and diplomatic channels, the sanctions and coordinated Western response represent political escalation that unnecessarily heightens tensions and contradicts stated commitments to engagement. Beijing has consistently framed the accusations as evidence of anti-China bias in Western intelligence assessments rather than legitimate security concerns.
Salt Typhoon revealed that even the world’s most sophisticated intelligence alliance, facing the world’s most aggressive cyber adversary, operates with fundamental coordination failures, regulatory incoherence, and philosophical contradictions that compound rather than contain the damage.
Why Hardware Must Replace Software
The most alarming aspect of Salt Typhoon is not what happened but what continues to happen.
CISA Executive Assistant Director Jeff Greene stated plainly: We cannot say with certainty that the adversary has been evicted, because we still don’t know the scope of what they’re doing. Senator Maria Cantwell’s December 2025 assessment was equally stark: Telecom companies infiltrated in the attack have failed to prove the Chinese hackers have been eradicated from their networks.
AT&T and Verizon announced in January 2025 that they had successfully expelled the attackers from their networks, with Mandiant providing independent verification. The claims met immediate skepticism from government officials and security experts. The skepticism has not been resolved. When Senator Cantwell demanded documentation, the carriers could not provide evidence that Chinese hackers had been fully removed.
The technical reasons for persistent access are well understood.
Salt Typhoon’s persistence mechanisms, including GRE tunnels on network devices, Demodex kernel rootkits, and modified authentication server configurations, can survive standard remediation procedures. The attackers’ average dwell time of 393 days before detection, with some environments compromised for over three years, demonstrates operational security sufficient to reestablish access even after apparent eviction. If the attackers anticipated discovery, they likely created backup persistence mechanisms that remediation teams have not found.
Read the rest here and consider subscribing.